TPM is a chip that provides control over what software can or cannot run on the computer. The argument is that this provides a high level of user security and industry digital rights management. If only good software is allowed, bad software (such as malware and illegally downloaded videos and software) cannot run. The current version of TPM is selectable – the user can choose to opt in or opt out of its use.
The problem with version 2.0 is that it is controlled by the operating system and always on. German publication Zeit Online has seen a number of government documents that indicate growing concern among German federal agencies. The problem focuses on three issues: firstly, TPM 2.0 is default on; secondly, the user cannot opt out; and thirdly, it is controlled by the operating system – that is, Windows 8 and Microsoft.
Zeit quotes from a document produced by the Ministry of Economics as long ago as early 2012, which concludes, “The use of ‘trusted Computing’ technique in this form…is unacceptable for the federal administration and the operators of critical infrastructure.” The perceived danger is that Microsoft, a US company, could secretly be compelled either by existing or future US legislation, to hand the TPM keys over to the NSA. That would effectively be giving the NSA a permanent back door to all Windows 8 TPM 2.0 computers that could never be closed; nor even monitored to see by whom or when it was being used.
But Zeit suggests that the potential problems go even further. Quoting professor Rüdiger Weis from the Beuth University of Applied Sciences in Berlin, it suggests that the TPM keys could be intercepted in the country of chip manufacture – China. Theoretically, then, any user of Windows 8 with TPM 2.0 could be handing the computer’s entire contents to either or both the NSA and the Chinese authorities, without ever being aware of it.
Virtually Unbreakable
“We apply our BrainTrust™ proprietary video encryption to your movies before we upload them to our servers. If someone ever was able to gain access to your content, the files would be useless and unplayable, because they are stored in a scrambled, encrypted format. Once downloaded to the user’s hard drive, the files are still encrypted and only readable via the MOD Machine Player by a legitimate owner. We are not aware of a better DRM scheme than ours. Where Windows Media DRM is easily crackable, and doesn’t run on Macs, BrainTrust™ works great on Windows 8, Vista, Windows XP and Mac, and is virtually uncrackable.”
Virtually uncrackable? Well, since they load the file from a Python script, it’s easy to make a copy of the “decrypted” file before it’s reverted. Having done so, I was curious to see the encryption scheme. By comparing the binary files, I discovered the “proprietary video encryption” algorithm: for the first 15kB, each 1kB block has its initial bytes xor’d with the string “RANDOM_STRING”. That’s the “scrambled, encrypted format” that leaves these files “useless and unplayable”.
I fail to understand how reasonable knowledgable people can think that there’s some way of delivering information to a person without actually “Delivering the Information”! If you’re providing me with the video/music/text, in whatever format, in whatever encryption, and then you provide me with a key and/or player program, you ARE PROVIDING ME WITH THAT DATA!
The “security” around my content can be broke, it will be broke and there’s no way in hell that anything built under this logic is unbreakable. Because you’re not trying to keep the information safe from me, you’re just trying to control how i can access it. So you’re forced to surrender a way of rendering it “readable” but then you try to control when or how i can read it. Does any of this seem any logic to anyone?
“Hey, here’s my encrypted book, and here’s a key for decrypting it, but be advised you may only read it at daytime.”
What will stop me from reading it at night? Even if the letters in the decryption key or book were only visible at daytime due to some magic ink, why couldn’t i just make a copy of it at daytime and read it at night? If this kind of reasoning and problem thinking seems ridiculous to you, congratulations, you’re a giant step ahead than the entire Media Industry executives, worldwide. (( And some software executives as well. Specially the Gaming executives… ))
Everyone that has given this two minutes of serious thinking will tell you that the only way to curb piracy is to offer a good service and value for money. Or simply abandon the current line of business and try to make your revenue in other related service line such as Support or Merchandising. It strikes me as unbelievable stupid that this kind of “unbreakable security” myth lives on and is relied upon.
Hotmail: Your password was too long, so we fixed it for you
My previous password has been around 30 chars in size and now, it doesn’t work anymore. However, I could login by typing just the first 16 chars.
This limitation is well known (see Graham Cluley’s excellent post on the password limits of various services) however, what caught my attention was that by cutting the password to 16 chars, it would work.
To pull this trick with older passwords, Microsoft had two choices:
* store full plaintext passwords in their db; compare the first 16 chars only * calculate the hash only on the first 16; ignore the rest
Storing plaintext passwords for online services is a definite no-no in security. The other choice could mean that since its inception, Hotmail was silently using only the first 16 chars of the password.
To be honest, I’m not sure which one is worse.
Microsoft: Screwing up security and best-practices since, basically, ever!
I assume there’s nothing wrong with the water up there in Redmond, so why do MS keeps doing this kind of stupid things and just not giving an jota about security? Or Standards? Or just good engineering?
Another good example is this one:
@bphogan: Example of NIH: Microsoft PowerShell: “New-item foo.txt -type file” instead of ” touch foo.txt”
Microsoft could just have implemented some sort of POSIX compliant shell (( bash, zshell, and endless others )) all freely available, all standards compliant and all widely used in every other OS in the world. Instead they have to go and reinvent the wheel and do some half-baked effort, that probably is way more limited, way more insecure and always halfway but never there.
Update: To answer the original poster, apparently is the last one, MS has always only stored the first 16 characters of your password and simply ignored all the remaining ones.
Anonymous declares war after French firm trademarks its logo
“A French company trying to trademark the Anonymous logo and slogan for commercial purposes has inspired an angry response from a team claiming to be affiliated with the hacking group.
The company Early Flicker, or E-Flicker, has registered the headless man logo and the slogan ‘We are Anonymous, We do not forgive, We do not forget. Expect us’ with the French National Institute of Industrial Property. This would allow the company to produce and sell merchandising bearing the logo, and potentially to take action against others who use it in France.”
Either this is some sort of plot & honeypot by the French Intelligence or these are the dumbest business owners on Earth. (( I would say the first option but every time i’ve said “nobody is that dumb!” i’ve been proven wrong. ))
Keylogger Virus Hits U.S. Military Drones
“And, so far, the military has been unable to stop the virus/keylogger on a widespread scale. Repeated attempts to remove the malware from Creech’s computers have only proven temporarily successful, if that. As a kind of last resort, military network specialists have resorted to full drive wipes to combat the persistent infection. They have been using a tool called BCWipe to completely erase the hard drives’ data before rebuilding the drives’ contents back from nothing.
“We keep wiping it off, and it keeps coming back,” said an anonymous source to Shachtman. “We think it’s benign. But we just don’t know.””
You’ve got to be kidding. How is any virus/keylogger that can’t be eradicated benign?
I can just see it. The white-hat hacker spending endless nights in front of his machine, coding, tweaking, making redundant features so it can’t be erased, and in the end he writes the payload:
Imagine there’s no Heaven;
It’s easy if you try;
No hell below us;
Above us only sky;
[…]
Yep. It makes perfect sense. And what’s great about it is that it just spread to the control of armed with precision explosives flying autonomous vehicles. No harm can come from there right?
And if you have any problems with the keylogger virus, just unleash Skynet on it. I’m sure “she” can quell that nuisance for you.
When you thought you couldn’t see anything stranger (and dumber) than fiction, then comes reality…
Sustainable Softworks Blog
“The combination of application sandboxing and entitlements could provide a more elegant solution if it is applied carefully. Apple doesn’t need to solve the entire problem all at once, but it does need to recognize there are important applications beyond self contained productivity or entertainment, and begin thinking about how to include some of them in the Mac App Store.
To help get the conversation started, I’d like to suggest a rating system similar to the already familiar film-rating system:
“G” for General use or everyone
“PG” for Parental Guidance suggested (security implications should be noted, such as anything that installs a plugin)
“R” for Restricted (requires more extensive system access such as a backup or disk utility)
The point here is that Apple could offer a better user experience by allowing a broader range of integrated solutions to be offered in the Mac App Store.”*
Yes. The one approach fits all is in itself a security risk as more and more users and apps opt-out of the Mac App Store (MAS) entirely or circumvent its restrictions. Add to this the updated delay for security bugs most apps have – comparing with the non-app versions – this might blow up in Apple’s face. But read the full post at the source to get a better view of what’s being criticized
I usually just try to use the non-MAS versions for these reasons as well. And i find the all “download dmg file -> open it -> drag the app to where you want it” not that cumbersome, but then again, i’m not the usual Mac user so my view is skewed.
But Apple needs to seriously consider the criticism being stated all around the developer’s internet. Switching Preference Panes for a Menu Bar icon is, on the long run, a dumb idea. What happens when people have more than 10 apps that require this “hack”? Stop buying apps at the MAS entirely?
Quicklook your install packages
One of my biggest complaints and pet-hates are the Install Packages many developers feel they must include. (( I always have the impression they’re just Windows developers that transitioned to the Mac without fully understanding it. ))
The problem is that Install Packages are a security and abuse issue waiting to happen. You are required to go back to the “dark ways” and just mindlessly click “next, next, insert password, next…”
to go through screens of useless information while the installer package can simply be wiping out your home folder and installing a key logger on a system level and you will never even know what it did.
A possible solution to this is a Quicklook plugin called “Suspicious Package“, a very apt name i must add. With it you can simply invoke Quicklook (( through pressing the space bar on finder or right-clicking it and selecting on “Quick Look filename” )) on a Install Package and see what its contents are.
You will now see where the installer will install files, if it haves any install scripts (and you can look through these if you understand them) or if they require an Admin password or a full System Restart to install. All without even executing the file once.
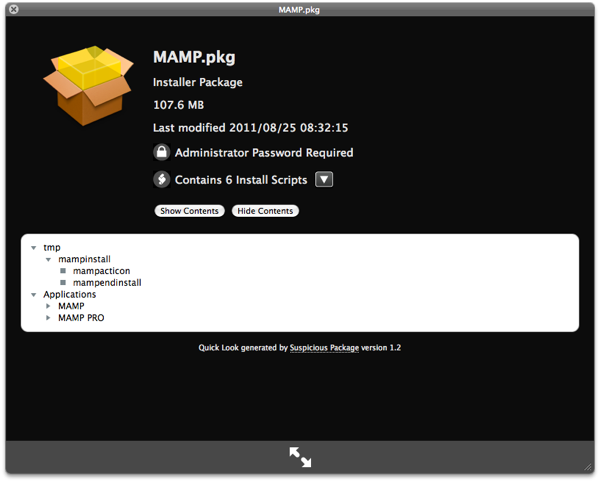
A QuickLook on the MAMP install package.
The installation of the plugin itself is very simple and you just need to drag the plugin to your Quicklook folder on YourUserFolder/Library/Quicklook . If no such folder exists just create it with the exact name of “Quicklook”.
It should be noted that although Mac OS X is a very secure system, it is no more secure than any other when it comes to the user allowing suspicious applications to run with the elevated privileges of a Administrator. If an application has that privilege, because you gave them to it by typing your admin password, then the app can do as it pleases with your system. So, always go for the paranoid side of things, specially the ones that you are not fully sure of its character. Better safe than sorry…
DigiNotar cleanup
“Description: Fraudulent certificates were issued by multiple certificate authorities operated by DigiNotar. This issue is addressed by removing DigiNotar from the list of trusted root certificates, from the list of Extended Validation (EV) certificate authorities, and by configuring default system trust settings so that DigiNotar’s certificates, including those issued by other authorities, are not trusted.”
About Security Update 2011-005
Apple finally corrects the DigiNotar mess that everyone else had already corrected. 10 days after it went public and another 4 or 5 after everyone else had already corrected it. Including Microsoft. Can’t say it’s a stellar record in rapid response to security threats by Apple.
So in case you didn’t read this post regarding how to clean up this mess by hand, please run “Software Update” in your Mac as soon as possible. It involves a system reboot though.
DigiNotar certificate security issue
“We’ve been made aware of a security issue caused by the Netherlands-based CA DigiNotar, who mistakenly issued a valid SSL wildcard certificate for google.com. The existence of this certificate, coupled with the implied lack of proper verification at DigiNotar, means that we consider it inappropriate that our systems continue to trust DigiNotar to issue SSL certificates.”
Apparently there is a rogue Google security Certificate being used somewhere out there on the Internet.
This is a major flaw, as this is the way your computer knows when “he” is actually talking to Google.com or Gmail or any other site belonging to Google, probably including Google Checkout as well.
Recommendation is that you should disable any security certificate from DigiNotar and the post tells you how to do it.
As warning, although i do believe this is a safe practice to do and i currently think that you should do it, i’m not completely sure of it. So decide for your own and do your research before.
The only apparent downside is that you may find some sort of “this website security certificate can’t be trusted” on other sites than Google. But if Google certificate got hijacked how safe do you think that website you’re apparently visiting is?
Update: Apparently Microsoft is also recommending removing DigiNotar Certificates from your computer, so never mind my initial objections.
